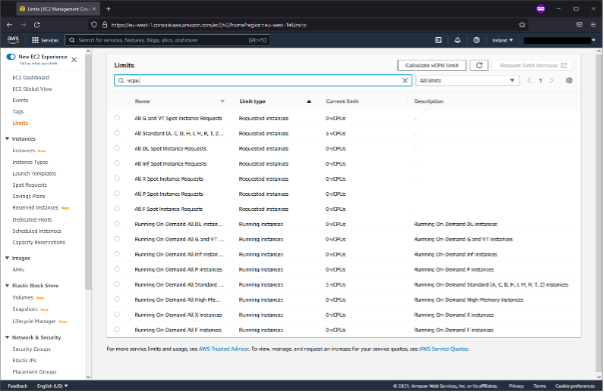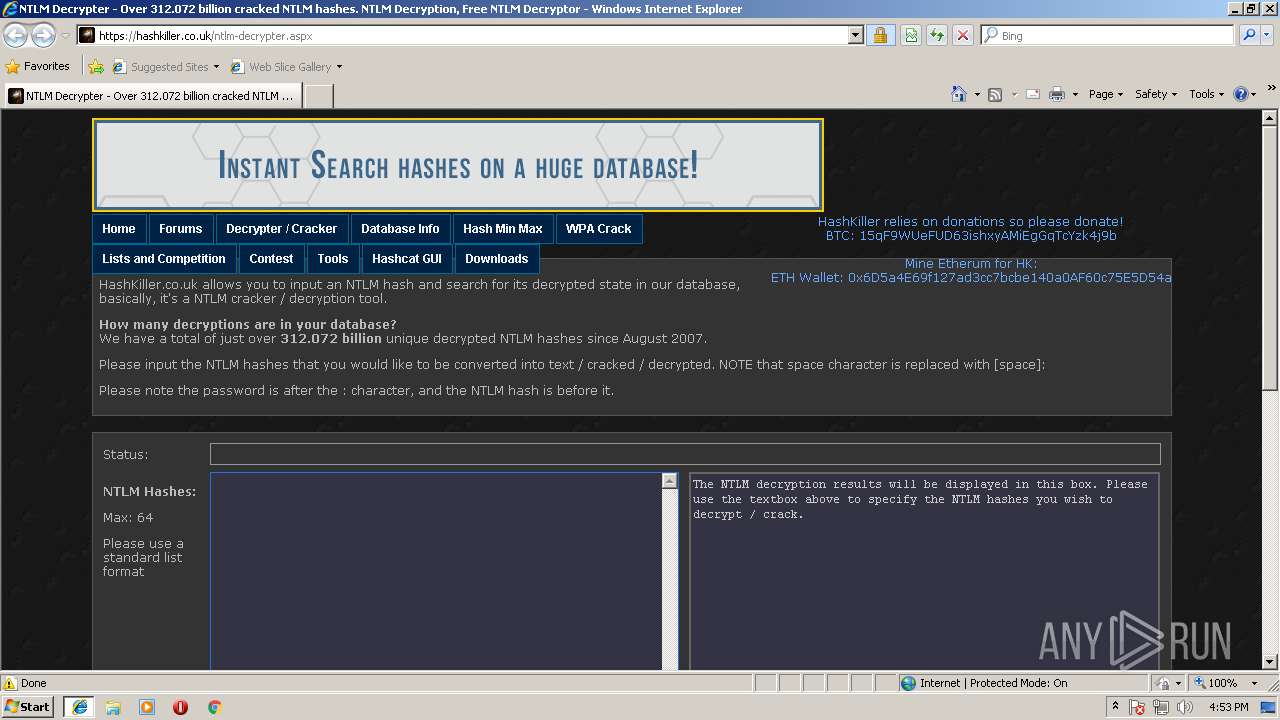
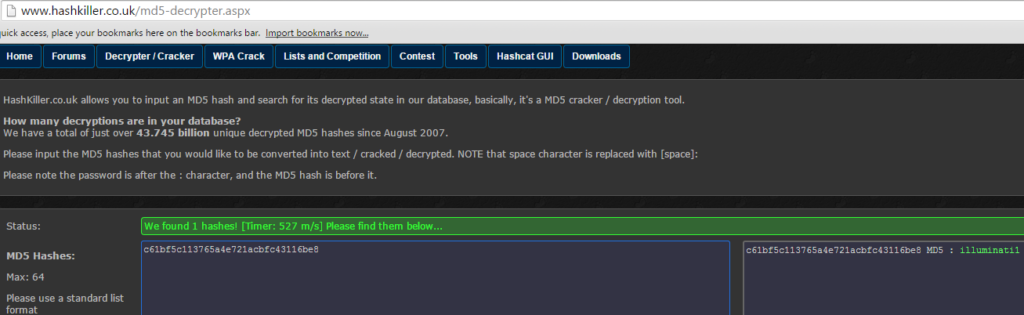
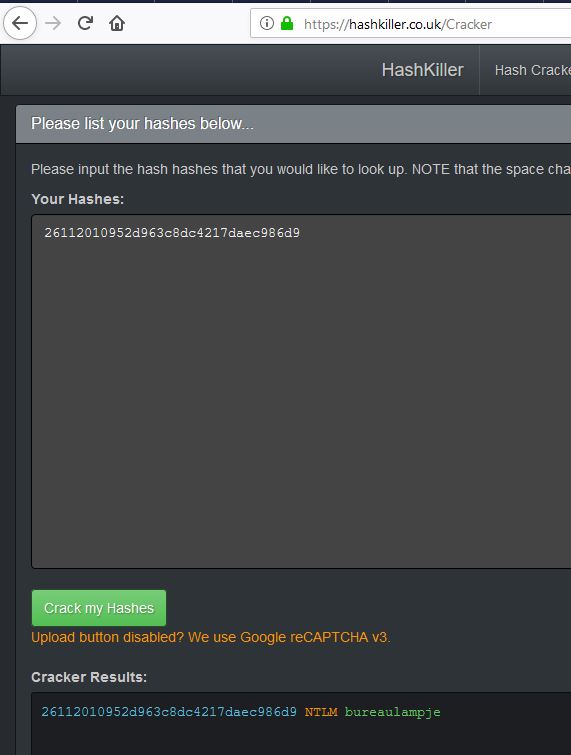
Malware analysis https://hashkiller.co.uk/ntlm-decrypter.aspx Malicious activity | ANY.RUN - Malware Sandbox Online
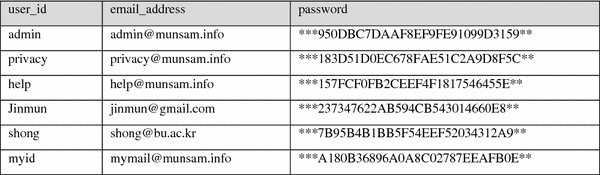
Proceedings of the 2018 International Conference on Machine Learning and Machine Intelligence: MD5 Secured Cryptographic Hash Va

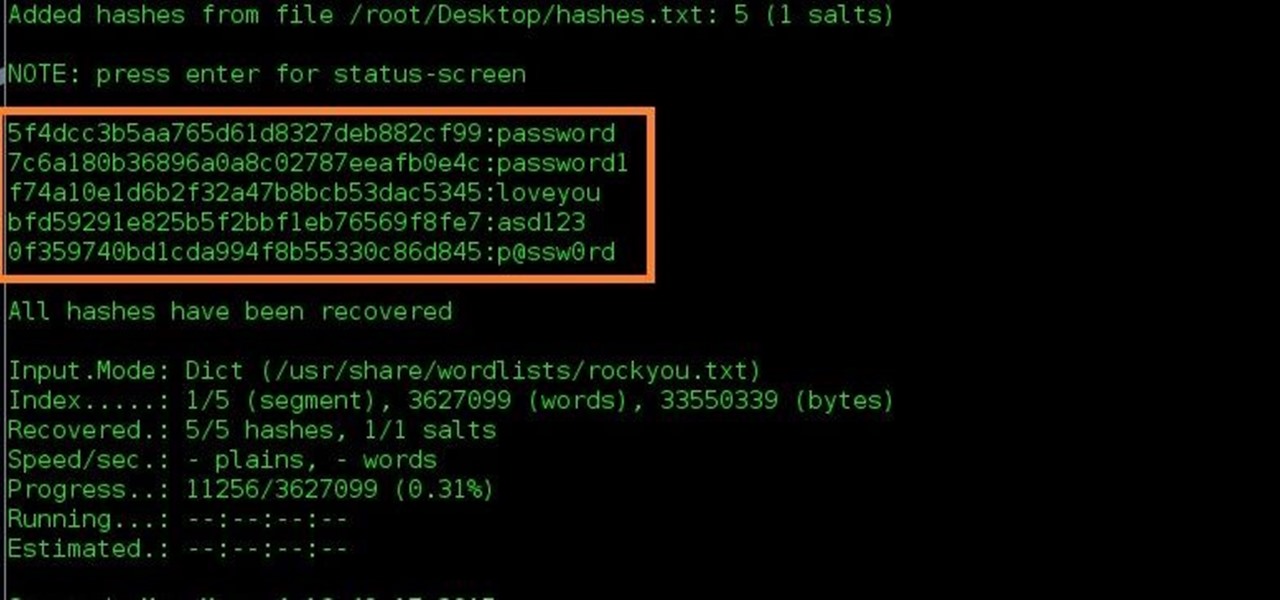
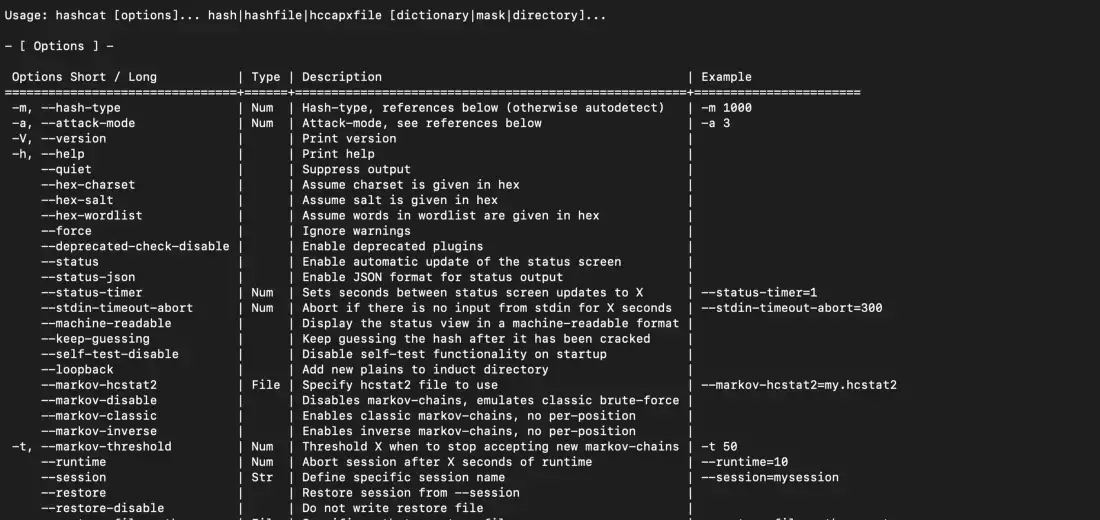
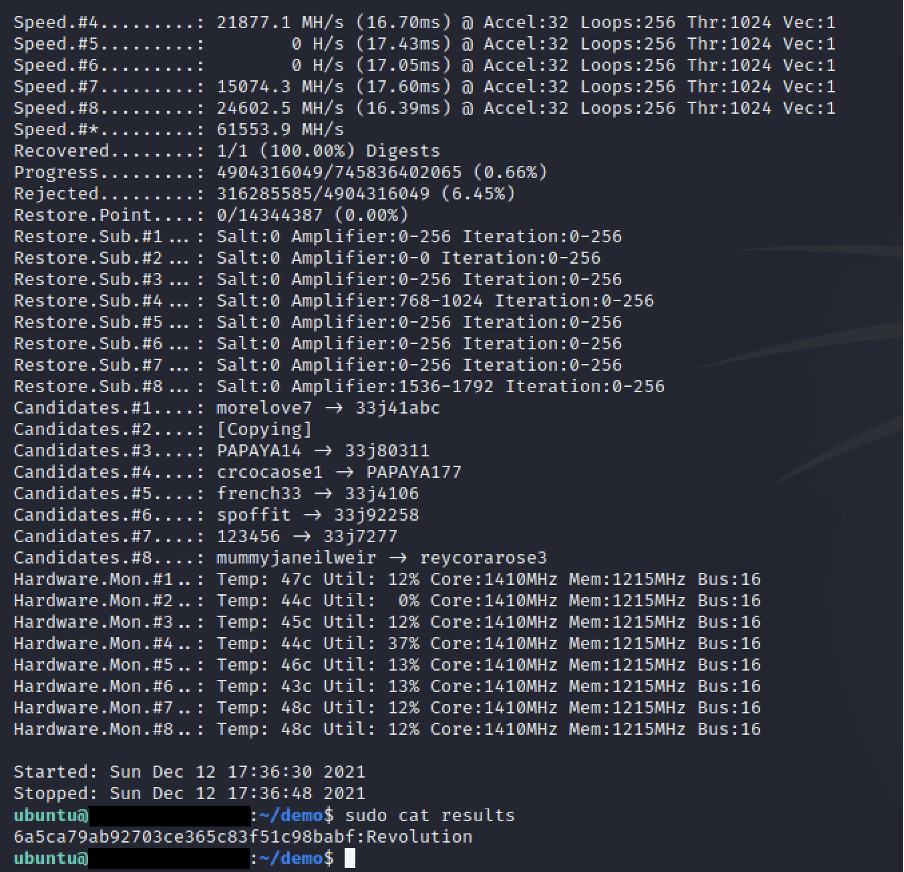
KALI – How to crack passwords using Hashcat – The Visual Guide | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022







![Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book] Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book]](https://www.oreilly.com/api/v2/epubs/9781787121829/files/assets/714fa5ac-a3a0-4378-b325-97dee1e71141.png)